Frequently Asked Questions
If you don't find the answer you need, contact us. You may be the one to save others.
Where do I find my API key?
See Find your API key.
Why are there unknown charges on my account?
Your API key may have been compromised, or you may have lost track of an automated process. If you have investigated and determined this is the case, here's how to fix it:
-
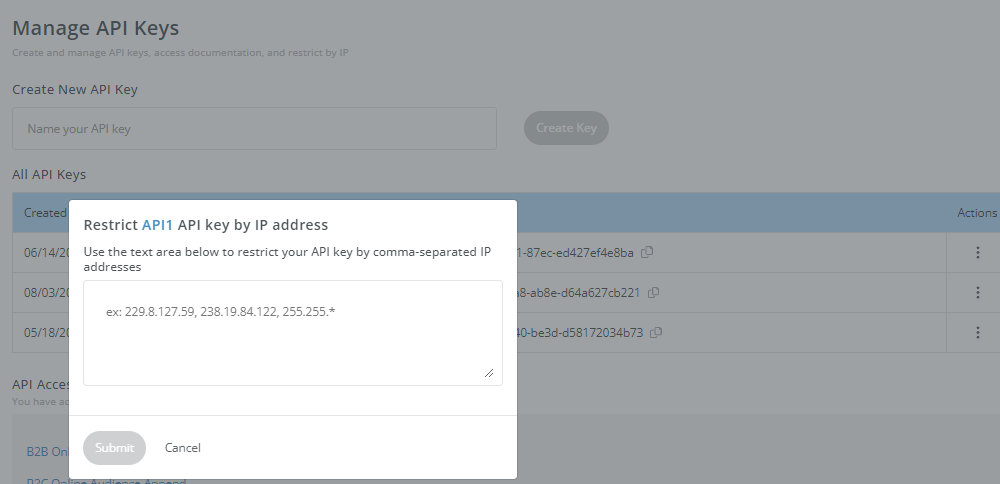
Set up IP Filtering on your API Key to ensure that only servers of known IP addresses can call the API
- go to your Manage API Keys, under the "Actions" column clic on the 3 vertical-dots beside your API Key and select "Restrict by IP" and add the know IP address authorized to use the API.
-
Deactivate your current API Key and generate a new key (see Find your API key), and keep it hidden... keep it safe.
Why does the API usage report page not correspond to the number of records sent via the API?
The REACH API servers log all inbound API requests into a database, and these are reported "as is" on the usage page. If any discrepancies are observed in the numbers, they may often be caused by duplicate API requests sent to our servers. We recommend reviewing the code used for the API calls and suggest activating outbound logs to have a clear report on the outbound calls.
Note: REACH API logs are based on US Pacific Time and NOT UTC; this may also contribute to discrepancies in the reported numbers.
I have hashed emails - will that work?
Yes, the REACH APIs accepts SHA1, SHA256 and MD5 inputs. For details see Hashed Input Support.
Do you have data for businesses and people outside of the U.S.?
Versium REACH APIs currently support only US Data.
Why do I get different results from different APIs?
Each API employs match codes (either fuzzy or precise) and data sources (ranging from broad to highly reliable) tailored to your specific needs. As a result, identical inputs may yield numerous matches or none at all, depending on the API call.
Why does the API response time vary so mych?
Response time varies and is directly dependent on the API payload.
The APIs Response Timepage reports the average response time for each API. Depending on the payload (i.e., the data provided as input to the API), the response time will vary.
Developers can use the rcfg_max_time parameter to enforce a maximum allowed runtime (in seconds) for the API. For more details, please see Common Inputs and API Parameters.
Updated 3 months ago
